
Tiêu chuẩn ISO 27001 ra đời nhằm đáp ứng yêu cầu về hệ thống quản lý an ninh thông tin (ISMS), giúp các doanh nghiệp xây dựng quản lý một hệ thống thông tin an ninh, an toàn, hiệu quả.
Tiêu chuẩn này áp dụng cho tất cả các tổ chức không phân biệt quy mô hay lĩnh vực hoạt động nào, có nhu cầu quản lý, xử lý và bảo vệ thông tin.
Chứng nhận 27001 là một tiêu chuẩn với những yêu cầu khá khắt khe. Để đạt được chứng chỉ ISO 27001; Doanh nghiệp sẽ phải tốn rất nhiều thời gian và công sức.
Vậy Quy trình chứng nhận ISO 27001 gồm những bước nào? Cùng theo dõi bài viết dưới đây nhé!
Chứng nhận ISO 27001 đây là một tiêu chuẩn quốc tế về việc bảo mật thông tin và đưa ra được những đặc điểm kỹ thuật cho hệ thống quản lý an toàn thông tin (ISMS).
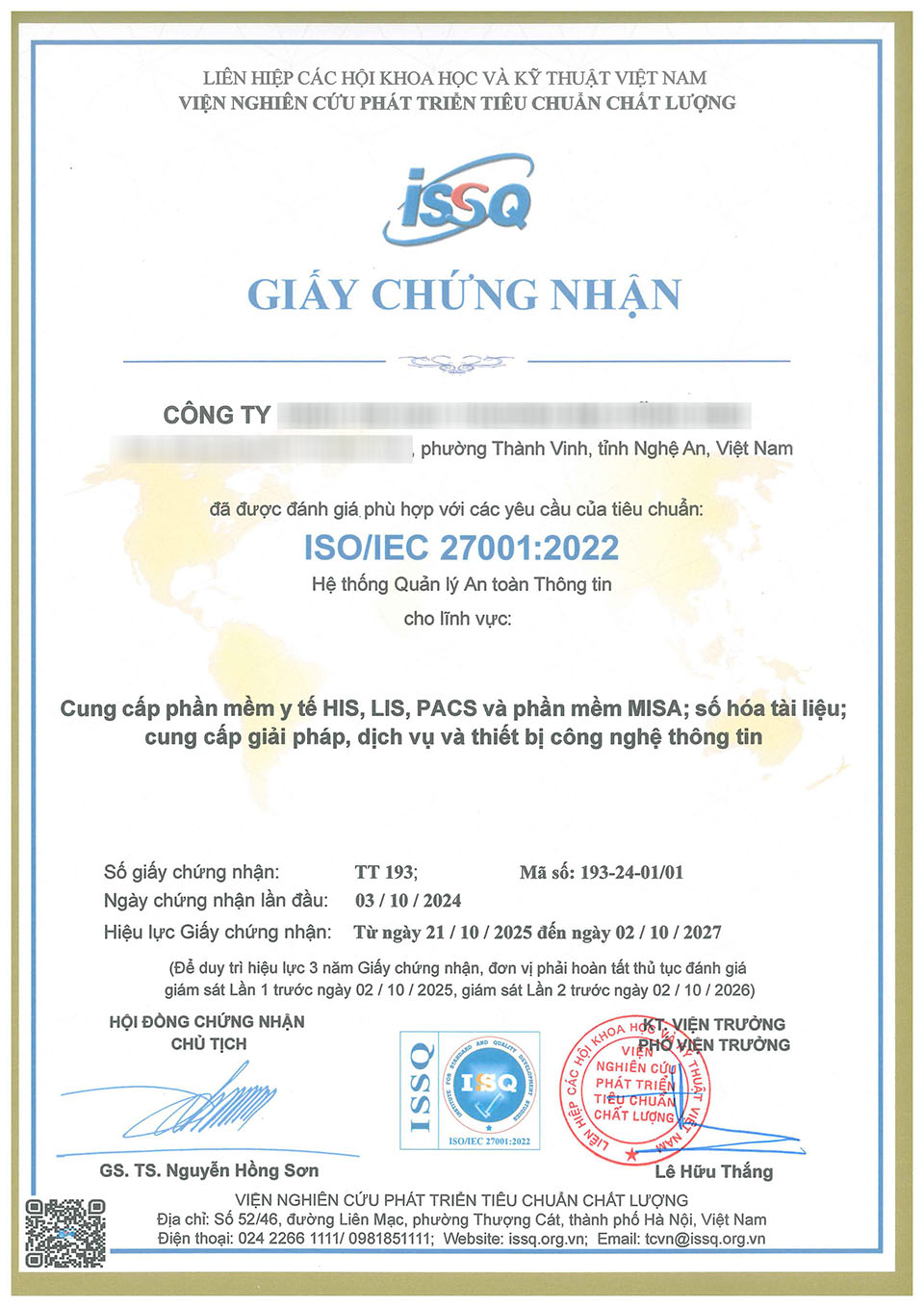
Tiêu chuẩn này là việc mà tổ chức chứng nhận (đánh giá bên thứ 3 – Viện chất lượng ISSQ) đánh giá một doanh nghiệp hay một tổ chức áp dụng cho hệ thống quản lý an toàn thông tin theo những điều khoản của chứng nhận ISO 27001.
Nói một cách khác, ISO 27001 được công nhận ở trên toàn thế giới đã cho thấy rằng ISMS của doanh nghiệp, tổ chức phù hợp với các phương pháp hay nhất về vấn đề bảo mật thông tin.

Quy trình chứng nhận ISO 27001 của Tổ chức chứng nhận trải qua các bước sau. Các bước như vậy sẽ đảm bảo rằng chứng nhận là khách quan và phù hợp với các yêu cầu của tiêu chuẩn.
Mục đích trao đổi thông tin giữa tổ chức chứng nhận và khách hàng nhằm đảm bảo các thông tin trao đổi trước đây giữa hai bên là nhất quán, đảm bảo rằng việc đánh giá chứng nhận sẽ phù hợp với các yêu cầu của Tiêu chuẩn và của khách hàng. . Thông tin trao đổi bao gồm:
Doanh nghiệp sẽ gửi tổ chức chứng nhận gồm: Các tài liệu, hồ sơ liên quan đến việc áp dụng tiêu chuẩn ISO 27001.
Tổ chức chứng nhận cử chuyên gia trong lĩnh vực tương ứng đánh giá hiện trạng hồ sơ ISO 27001 để phát hiện những điểm yếu trong tài liệu và việc áp dụng hệ thống ISO 27001 trong lĩnh vực này.
Sau bước kiểm tra và đánh giá sơ bộ. Chuyên gia phải chỉ ra được những tồn tại về hệ thống tài liệu và thực tiễn áp dụng ISO 27001 cần chấn chỉnh để doanh nghiệp khắc phục kịp thời. Bước đánh giá sơ bộ này rất có lợi cho tổ chức, doanh nghiệp. Bởi vì nó phục vụ như một hướng dẫn mẫu cho quá trình đánh giá chính thức.
Doanh nghiệp được cấp chứng nhận ISO 27001 nếu tất cả các tài liệu phù hợp với thực tế. Và tất cả những điểm không phù hợp đã được khắc phục thỏa đáng. đồng thời được trưởng đoàn đánh giá xác nhận.
Hệ thống quản lý bảo mật thông tin (ISMS) là một cách tiếp cận có hệ thống để nhằm quản lý thông tin nhạy cảm của công ty bạn để giúp tăng cường bảo mật. Nó bao gồm con người, quy trình và hệ thống CNTT dựa trên quản lý rủi ro để giúp các tổ chức thuộc mọi quy mô và ngành giữ được an toàn cho tài sản kinh doanh ở dạng thông tin.
Với mức độ nghiêm trọng ngày càng tăng của các vụ vi phạm dữ liệu trong thế giới kỹ thuật số ngày nay, ISMS rất cần thiết trong việc xây dựng an ninh mạng của một tổ chức. Một số lợi ích của ISMS sẽ bao gồm:
Quy định chung về bảo vệ dữ liệu (GDPR) có phạm vi rộng hơn nhiều so với Đạo luật bảo vệ dữ liệu (DPA) trước đó và được thiết kế để phù hợp với bối cảnh kỹ thuật số hiện đại. Quy định này đặt ưu tiên nhiều hơn cho dữ liệu của các cá nhân và yêu cầu các tổ chức xây dựng các chính sách và thủ tục để xác định và áp dụng các biện pháp kiểm soát kỹ thuật và tổ chức có liên quan để bảo vệ dữ liệu. cá nhân.
GDPR áp dụng cho hai loại người dùng, điều này chắc chắn sẽ giảm bớt tất cả; Bộ điều khiển và bộ xử lý. Tóm tắt; bộ điều khiển sẽ xác định cách thức và lý do dữ liệu cá nhân được sử dụng hoặc xử lý trong khi bộ xử lý hoạt động thay mặt cho bộ điều khiển, giống như các tổ chức phụ thuộc vào dịch vụ của nhà cung cấp dịch vụ CNTT. Bộ xử lý có nhiều nghĩa vụ pháp lý hơn đối với khách hàng trong trường hợp vi phạm, nhưng bộ kiểm soát sẽ chịu trách nhiệm đảm bảo rằng các hợp đồng với bộ xử lý tuân thủ GDPR.
Đây không phải là một tài liệu đầy đủ về quy định và không nên được sử dụng như vậy. Tìm hiểu các điểm chính và yêu cầu của chứng nhận ISO 27001 tại đây.
Trên đây là những chia sẻ của Viện chất lượng ISSQ về Quy trình chứng nhận ISO 27001 - Hệ thống an toàn thông tin
Hy vọng qua bài viết sẽ cung cấp được các thông tin hữu ích cho bạn và doanh nghiệp của bạn.
Viện Chất lượng ISSQ luôn sẵn sàng đồng hành cùng Quý cơ quan, doanh nghiệp trong thời kỳ hội nhập và phát triển.
Vui lòng liên hệ đến hotline: 0981851111 hoặc vienchatluong@issq.org.vn | tcvn@issq.org.vn chúng tôi rất hân hạnh được phục vụ quý khách hàng!.
Ngày đăng: 15/04/2023